Міжнародна конференція HACKIT, присвячена кібербезпеці, об'єднує велику кількість білих хакерiв, інвесторів та компаній, що працюють у сфері безпеки. Завданням нашої команди було розробити фiрмовий стиль, вiдео та сайт, якi привернуть увагу до конференції людей з різних країн.

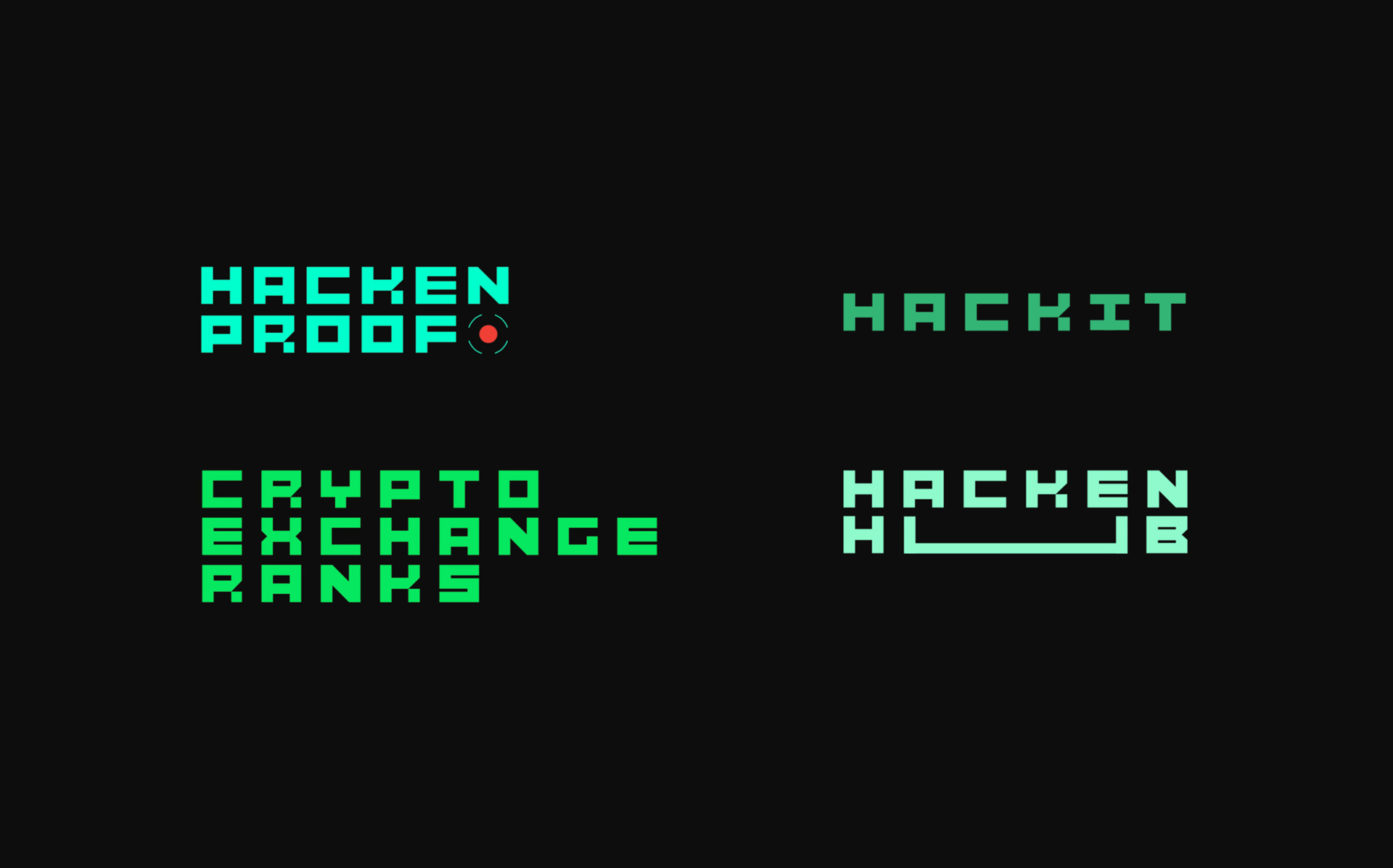
Ми розробили шрифт, на основі якого можна легко створювати логотипи для нових проектів Hacken. Конференція HACKIT не стала винятком. На основі шрифту ми створили інтерактивний логотип, який взаємодіє з аудиторією та втягує їх у гру.

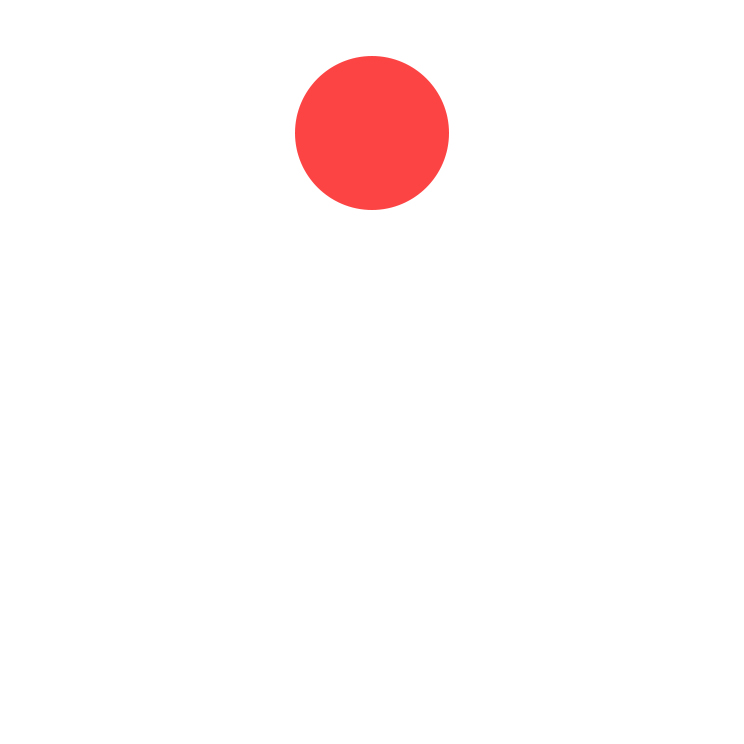
Червона мітка — один з головних елементів, який використовується у фірмовому стилі та сайті, асоціюється зі снайперським прицілом або зі знаком запису/стеження (REC). Вона символізує вразливе місце в складній, багатоступеневiй системi.


У роботі з текстом все побудовано на контрасті: заголовок і основний текст.
В оформленні використовуємо прийом дублювання. Це пов'язано як з візуалізацією помилок, так і з бажанням показати багатошаровість елементів, що дає нам можливість заховати між шарами червону мітку.
Патерн будується на основі модульної сітки шляхом переміщення по ній окремих елементів. Він відсилає нас до стилістики Баухауса. Ми звернулися до неї, оскільки основи, на яких базується Баухаус, близькі якостям так характерним для хакерської аудиторії — фокус на головному, відмова від зайвого і необгрунтованого, конструктивність. У той же час графіка в стилі Баухауза часто нагадує логічні шаради — а це саме те, з чим мають справу хакери.
Сітка символізує процес сканування системи для виявлення небезпечних місць. Ця сітка i допомагає виявити вразливість — червону крапку.
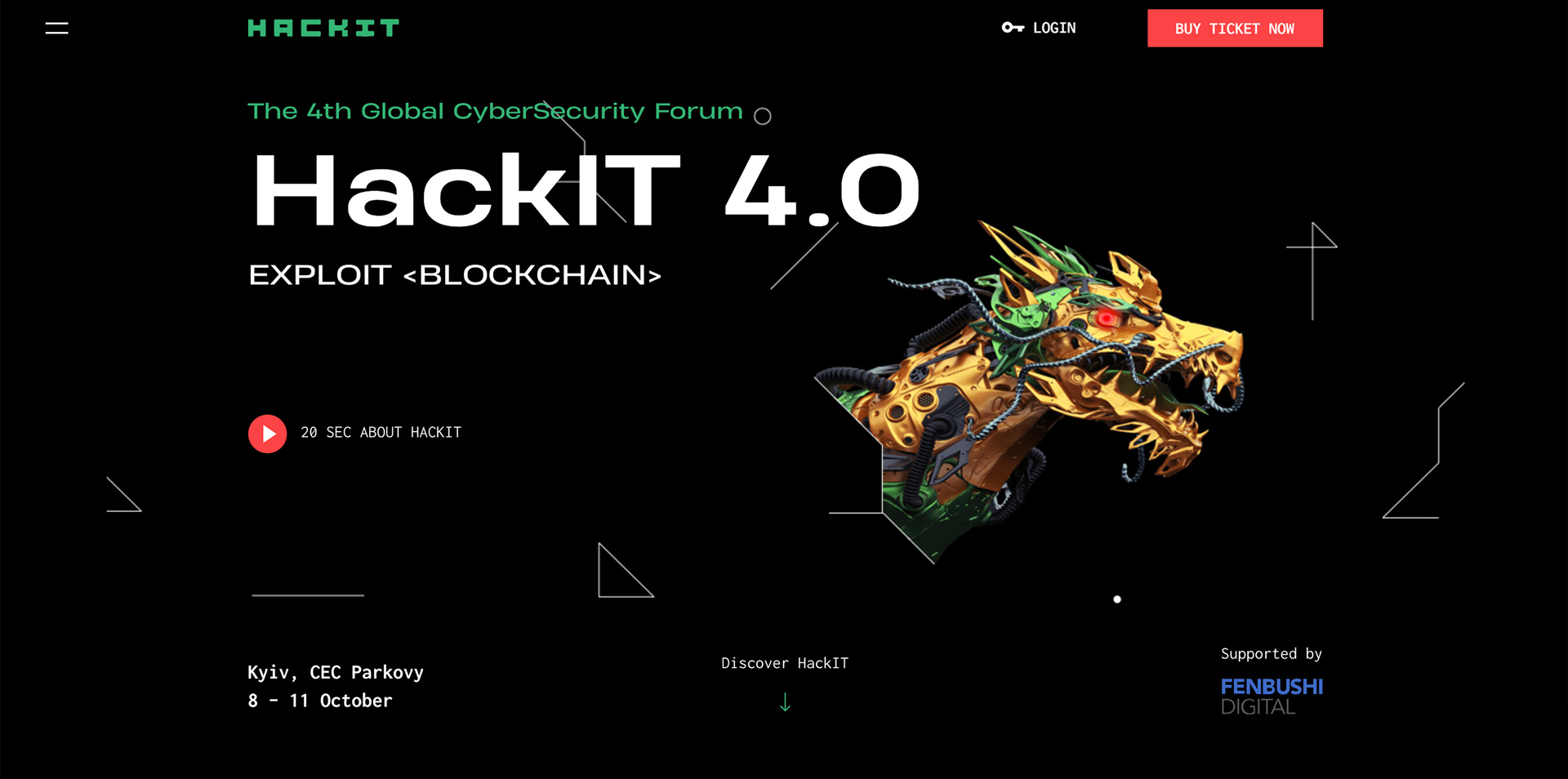
Образ дракона є ключовим для HACKIT 2018. Дракон символізує противника, челлендж, ребус, який потрібно вирішити, а якщо більш буквально — сервіс, сайт, мережу, в яких хакер шукає вразливість.
Для оформлення фотографій ми використовуємо метод дублювання зображення — такий навмисний глітчевий ефект асоціюється з багами та помилками. Тут ми також використовуємо багатошаровість, щоб заховати в шарах червоні мітки.



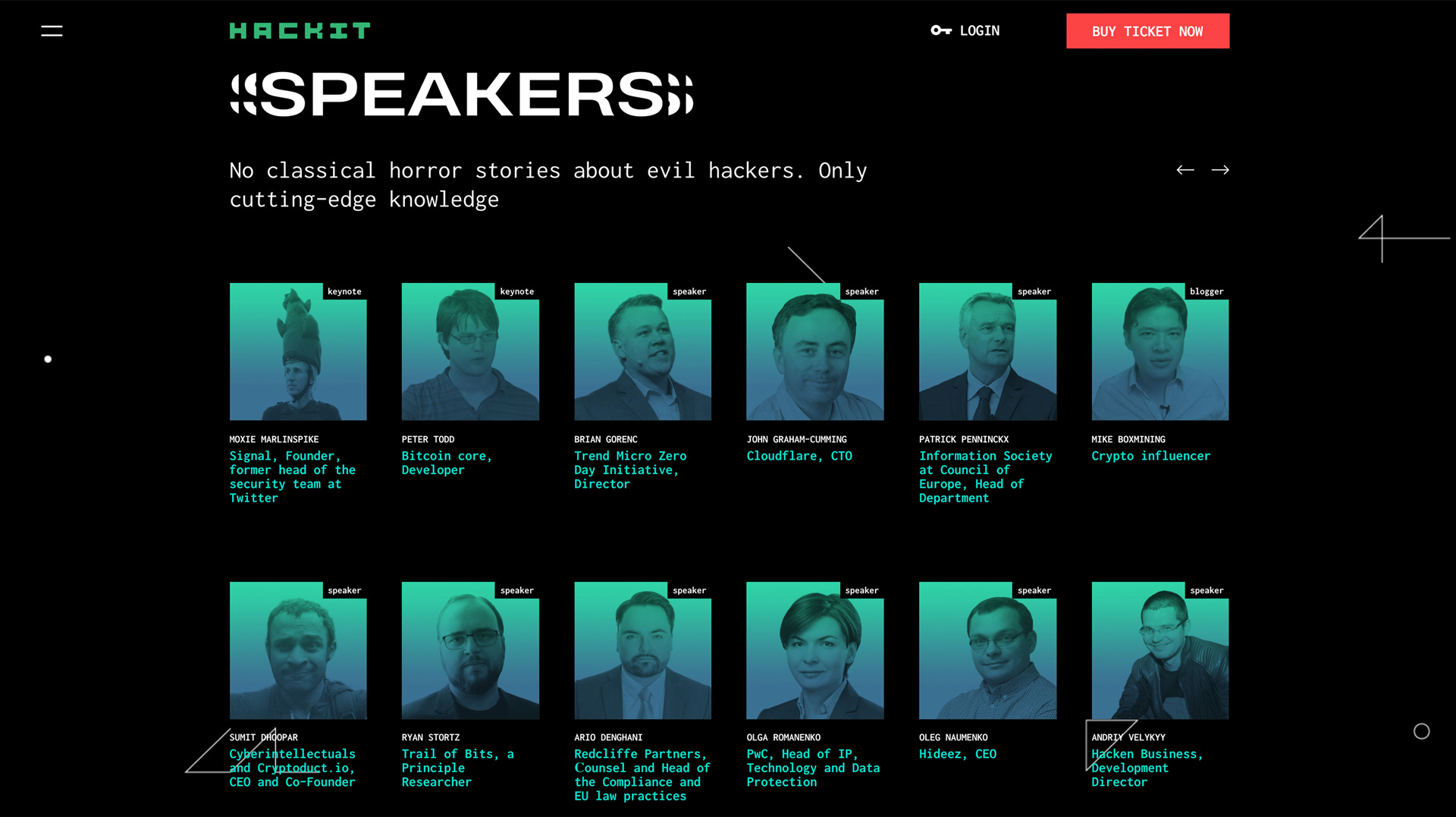
Для оформлення віжуалiв ми використовуємо накладення кольорового градієнта.

Ми створили впізнавану виразну стилістику, розробили цілий ряд нових, яскравих, емоційних образів, які добре взаємодіють з цільовою аудиторією.

У дизайні ми намагались передати естетику світу хакерів, використовуючи нетривіальні методи. Веб-сайт містить ряд прихованих ефектів, які додають елементи гейміфікації, що спонукають аудиторію більш тісно взаємодіяти з сайтом.
Відео-тізер розповідає про наповнення конференції. Ми ставили перед собою мету в перші 5 секунд зацікавити глядача за рахунок ефектного й емоційного образу, а далі в максимально насиченому темпі показати всі ключові моменти. Кліповий темп відео дозволяє заховати в ньому приховані послання, які містять різні бонуси для глядача та підштовхують дивитися його неодноразово.